Install Noxen on macOS
Drag-to-Applications, first launch, and one-click license activation — the five-minute path from purchase email to a ready-to-scan Noxen install.
Before you start
Make sure your Mac meets the prerequisites — Noxen is a native macOS
app and uses several modern frameworks (CryptoKit for feed verification,
Network.framework for raw port scanning, SwiftData for
local storage). The system
requirements page has the full list, but the headline numbers are:
- macOS 14.0 (Sonoma) or later — Apple Silicon or Intel.
- SSH access to each host you want to scan (key-based preferred).
- An iCloud account if you want findings + host catalog to sync to the iOS companion. Optional — Noxen works fully offline without one.
Download
Noxen ships as a notarised .dmg served from
noxen.app/releases/. The latest stable build link
lives on the homepage; purchased licenses also
receive the same link by email from Lemon Squeezy.
Verify the download is the file we shipped — every release is signed with the Noxen Developer ID certificate and notarised by Apple. macOS Gatekeeper checks both before first launch; if either signature is missing, the dialog text changes from "Noxen.app is from a verified developer" to "unidentified developer", and you should not run the build.
First launch
Drag Noxen.app from the mounted .dmg
to /Applications, eject the disk image, then
double-click Noxen in Applications. macOS prompts once to
confirm the app is from a verified developer; choose
Open. From here on, Noxen launches straight
from the Dock or Launchpad like any other Mac app.
On first launch, Noxen shows a four-page welcome sheet that explains what scanning means, what data leaves your Mac (very little — see the privacy reference), and offers two opt-in toggles:
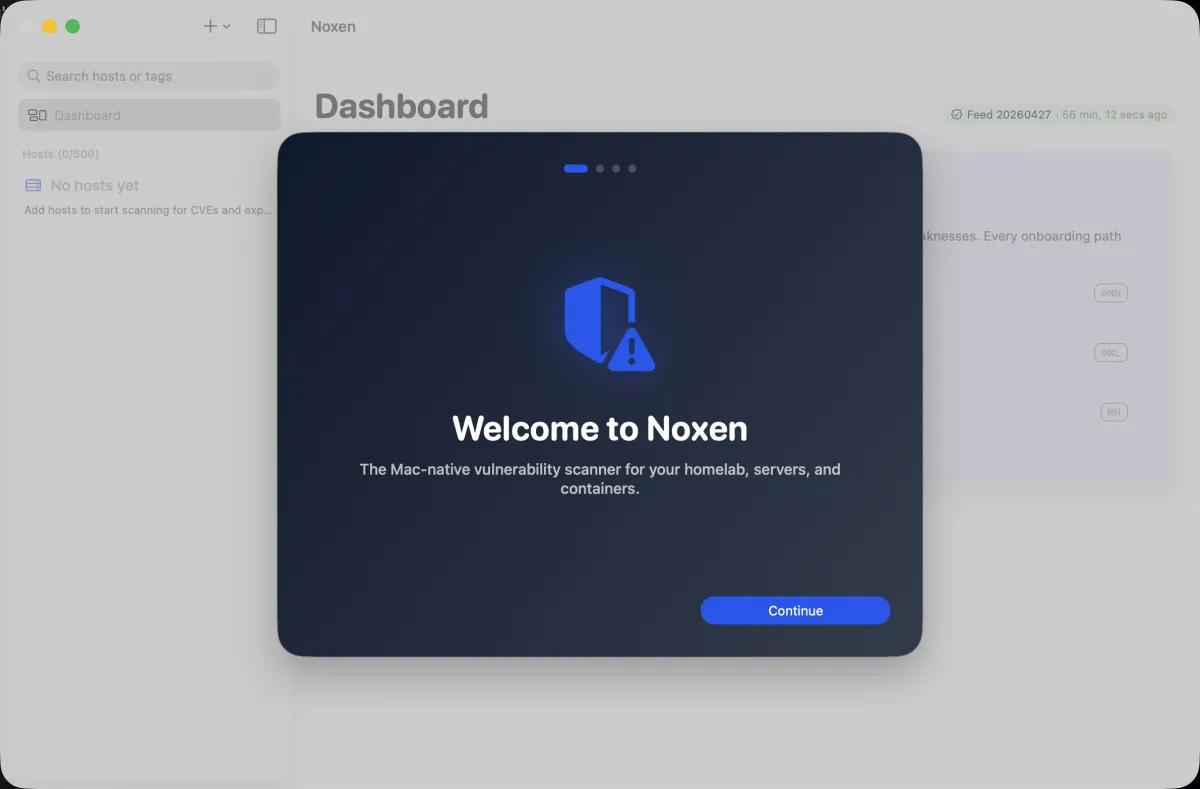
~/.ssh/config
import — both can be turned on later from Settings.- Download CVE feed now. Pulls the signed
~95 MB daily snapshot from
feed.noxen.appso the first scan has data to match against. Skipping this is fine if you're on a metered connection — the feed downloads automatically before your first scan instead. - Import hosts from
~/.ssh/config. Reads your existing SSH config and lets you choose which hosts to enrol. Wildcards (Host *.home) are skipped; only concrete hosts are offered. See SSH config import for the details.
Both opt-ins are reversible — toggle them later from
Settings → Account. Noxen never reads your
~/.ssh/config until you explicitly run the import,
and never sends host inventories to any server.
License activation
Noxen is free to use against up to 3 hosts. Beyond that, a one-time license unlocks 25 hosts (Noxen 1.x), and the Live Feed subscription unlocks 100 with daily-rebuilt CVE coverage — see pricing for the full tier matrix.
When you purchase a license, Lemon Squeezy emails an activation
key plus a one-click activation URL of the form
noxen://activate?key=…. macOS recognises the
noxen:// scheme and routes the click directly to
the running app, which writes the key into the macOS Keychain
and refreshes the entitlements pane.
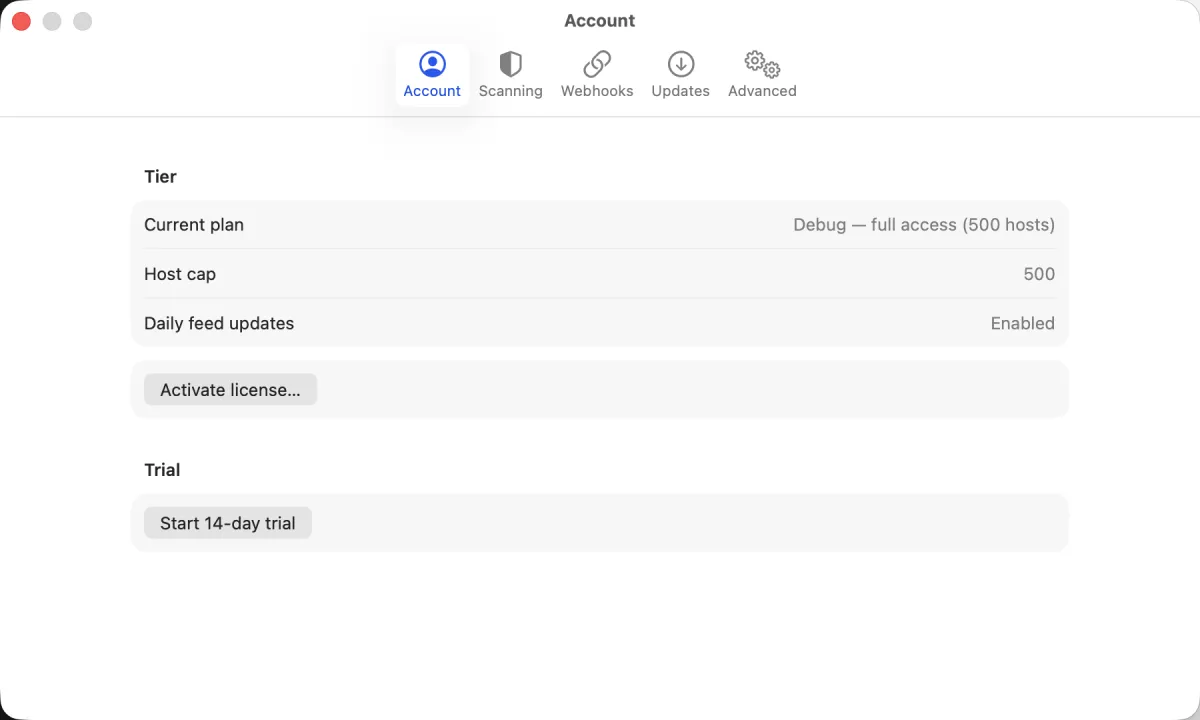
If the deep-link doesn't fire — for example, you're activating Noxen on a different Mac to the one that opened the email — paste the key manually:
- Open Noxen → Settings… (or press ⌘,).
- Switch to the Account tab.
- Paste the key into the Activate license field and click Activate.
If activation fails with "License key invalid or already used", the most likely cause is a copy-paste artefact (smart quotes, leading whitespace) — paste into a plain-text field first to inspect, then re-copy. License keys are machine-bound: a key activated on Mac A will refuse activation on Mac B until you deactivate from Mac A's Settings → Account pane first.
Verify the install
A successful install + activation lands you at the empty Hosts list with the + Add host menu in the sidebar, the host cap shown in the toolbar, and the CVE feed indicator either green ("up to date") or progress-spinning ("downloading"). If you skipped the feed download, the indicator stays grey until your first manual scan triggers it.
What's next
You're ready to add a host and
run your first scan, or jump straight to importing
from ~/.ssh/config if you have a populated
SSH config to enrol from.